1. essence 1: use hybrid protection and elastic bandwidth to replace a single long-term large bandwidth purchase, which is both cost-effective and safe.
2. essence 2: hand over core traffic to a provider with traffic cleaning capabilities, and offload non-core traffic through cdn and caching to reduce bandwidth optimization costs.
3. essence 3: reduce passive traffic exposure and reduce ddos protection costs from the source through strategic port restrictions and application layer optimization.
as a writer with many years of practical experience in network and operation and maintenance, i directly point out three major ways to save money: architecture optimization, operation strategy, and contract negotiation. for hong kong's 100g high-defense servers , don't blindly pursue high peak and large-diameter bandwidth. the correct approach is to combine cleaning capabilities and bandwidth flexibility.
the first step is to evaluate the real peak and attack model. based on historical traffic and attack logs, formulate hierarchical protection strategies and change the "large-diameter bandwidth" that only needs to be used during attacks to bandwidth-optimized flexible purchase or on-demand billing, which can save 40%+ costs in the long term.
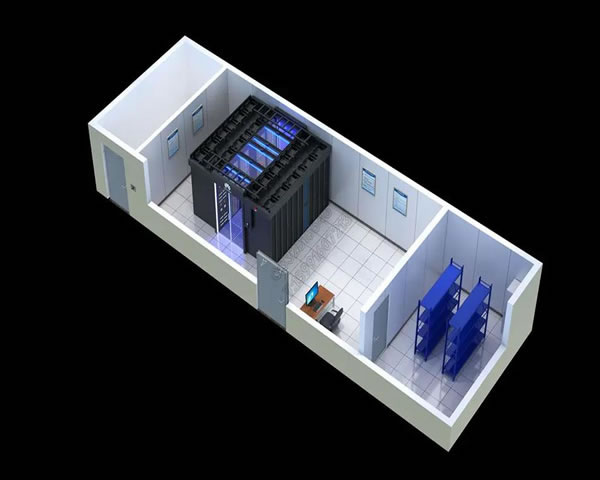
the second step is to adopt a hybrid cleaning architecture: the core business is bound to a high-defense server with 100g cleaning capabilities, and edge traffic is handled by cdn, waf and application layer caching. in this way, most of the garbage flow can be processed at the edge, avoiding all cleaning costs on the central caliber.
the third step is technical cost reduction: enable rate limiting, syn cookies, behavioral verification and intelligent ip reputation database filtering, combined with bgp black holes and policy routing, to slow down the attack in the early stages. these measures directly reduce cleaning bandwidth and computer room expenses by reducing traffic peaks.
the fourth step is that negotiation is as important as contract wisdom. agree with suppliers on elastic peak values, traffic cleaning thresholds, sla compensation and monthly settlement options to avoid one-time large upfront payments and over-commitment. use multiple suppliers to compare prices, and use the renewal period as a bargaining chip to get discounts.
the fifth step is data-based early warning and drills: regularly conduct stress testing and attack and defense drills, verify traffic distribution and clean links during ddos protection , record the cost and response time of each event, and adjust strategies to minimize costs and control risks.
step six: bonus points for compliance and trust: choosing a service provider with a local computer room or cooperative channel in hong kong can reduce additional transmission and delay costs. at the same time, the definition of responsibilities and log retention are clearly stated in the contract, which meets the professionalism and credibility required by google eeat.
finally, three quick tips are given: 1) close all non-essential ports and use the springboard host as the management port, 2) migrate static resources to cdn and enable compression and caching, 3) require peak and average segment billing on the bill. combining these methods, enterprises can maximize cost savings while ensuring business availability.
summary: to achieve "no loss of protection and sensible cost reduction" on hong kong's 100g high-defense servers , the core is to advance technology and business strategies in parallel - using hybrid protection architecture, elastic bandwidth, precise filtering and smart contract negotiations to achieve real cost reduction and efficiency improvement.
- Latest articles
- Practical Operation To Improve Alibaba Singapore Line Cn2 Connection Efficiency Through Reasonable Routing Strategies
- Technical Explanation: Can Hong Kong Vps Access The Internet? Comparison Of Implementation Methods When Using A Proxy Or Vpn
- Steps To Build Taiwan Native Ip Server Cluster From Scratch
- Contingency Strategies Multinational Companies Should Adopt When A U.s. Raid On Frankfurt Servers Becomes A Reality
- Holiday Peak Response Plan Protects Bilibili Taiwan Server
- Activation And Setting Tutorial: What Is The Hong Kong Native Ip Mobile Phone Card? Plug In The Card And Use It To Advance Apn Configuration
- Enterprise-level Japanese Native Ip Network Architecture Suggestions And Performance Optimization
- Summary Of Active Topic Statistics Of Japanese Website Sellers, Marketing Activities And Traffic Acquisition Hot Spots
- The Actual Exercise Verified Whether The U.s. High-defense Server Ignored The Attack Promise And Had A Feasible Solution.
- Where Is The Korean Server Of Warcraft Asia To Teach You How To Use Routing And Accelerators To Reduce Ping?
- Popular tags
-
From The Perspective Of Compliance And Audit, Look At What Hong Kong High-defense Servers Do To Meet Data And Operational Specifications
analyze the technical and process requirements of hong kong's high-defense servers from the perspective of compliance and auditing, covering ddos protection, cdn, vps/host, domain name management, audit logs and compliance certificates, etc., to help enterprises choose and purchase solutions that meet regulatory and operation and maintenance specifications. -
How To Choose Hong Kong 100g High-defense Server Bandwidth Configuration Based On Business Traffic
for different business types and traffic characteristics, this article introduces how to estimate bandwidth, select computer rooms and protection strategies when deploying 100g high-defense servers in hong kong, helping enterprises to strike a balance between cost and protection capabilities. -
Choose A Suitable Hong Kong High-defense Cloud Server To Improve Website Security
choose a suitable hong kong high-defense cloud server to improve website security, resist network attacks, and protect your data security.


